Links:
CheatSheets from Boll and Fortinet.
FortiOS 7.6 Downloads and Documents (Release Notes / CLI Reference)
FortiGate with FortiOS 7.6: First Configuration Steps
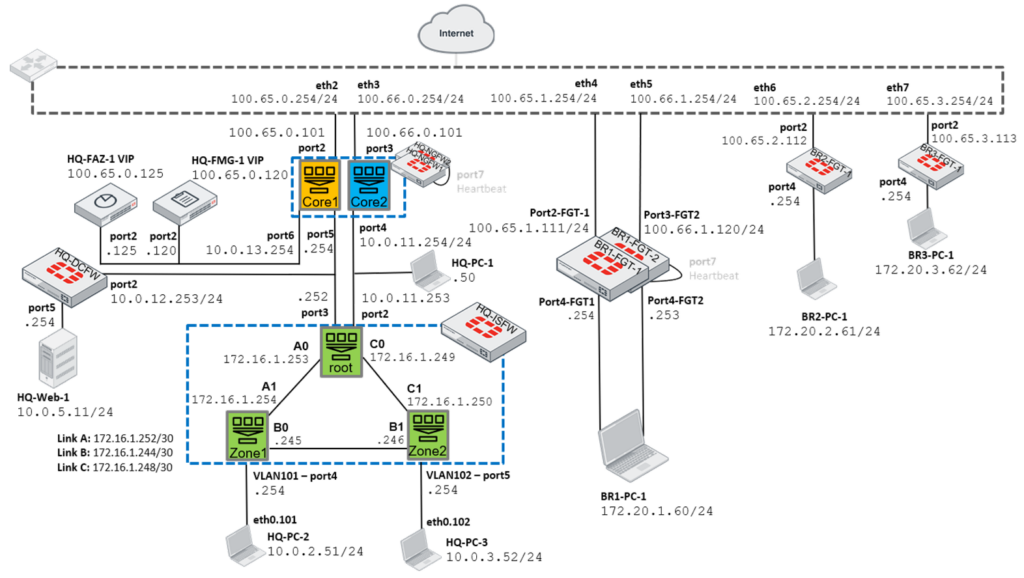
Lab Network:
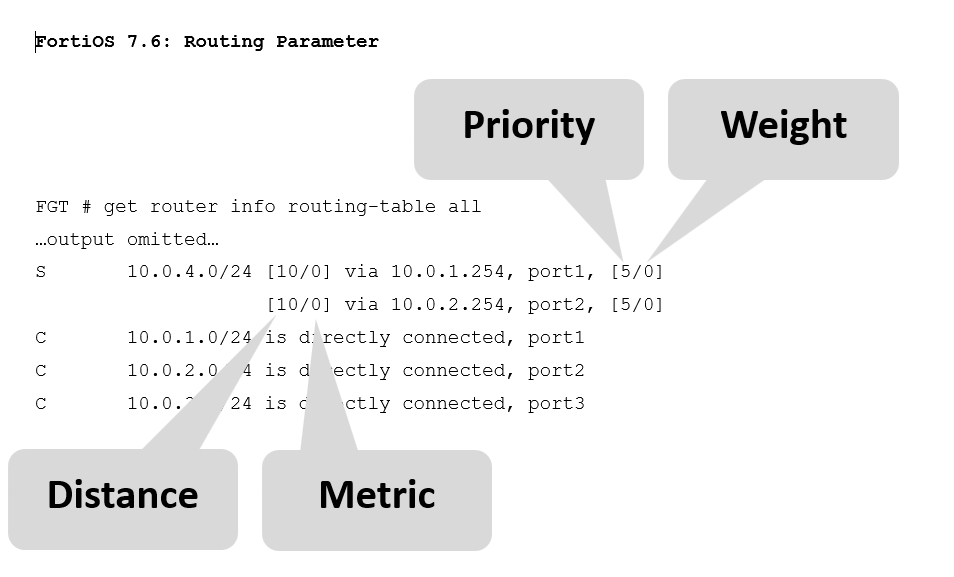
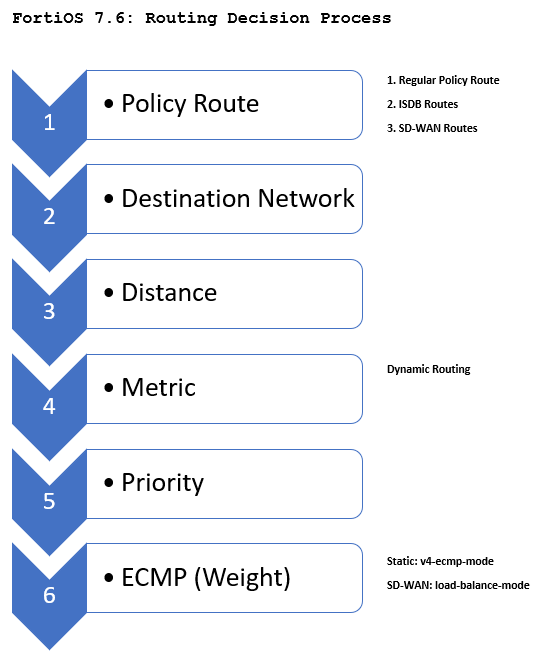
Chapter 5: Dynamic Routing Protocols
AS Numbers:
0 Reserved.
1-64’495 Public AS numbers.
64’496 – 64’511 Reserved to use in documentation.
64’512 – 65’534 Private AS numbers.
65’535 Reserved.
Additional Information
Flow versus Proxy Based Inspection
- Flow based (default)
- It is recommended that flow inspection is applied to policies that prioritize traffic throughput, such as allowing connections to be made towards a streaming or file server.
- Proxy based
- Because proxy mode provides the most thorough inspection, it is recommended that you apply proxy inspection to policies where preventing a data leak or malicious content is critical.
- Flow-based inspection takes a snapshot of content packets and uses pattern matching to identify security threats in the content.
- Proxy-based inspection reconstructs content that passes through the FortiGate and inspects the content for security threats.
Each inspection mode plays a role in processing traffic on route to its destination. While both modes offer significant security, proxy-based provides more feature configuration options, while flow-based is designed to optimize performance. More information on this topic is available in our Blog Post.
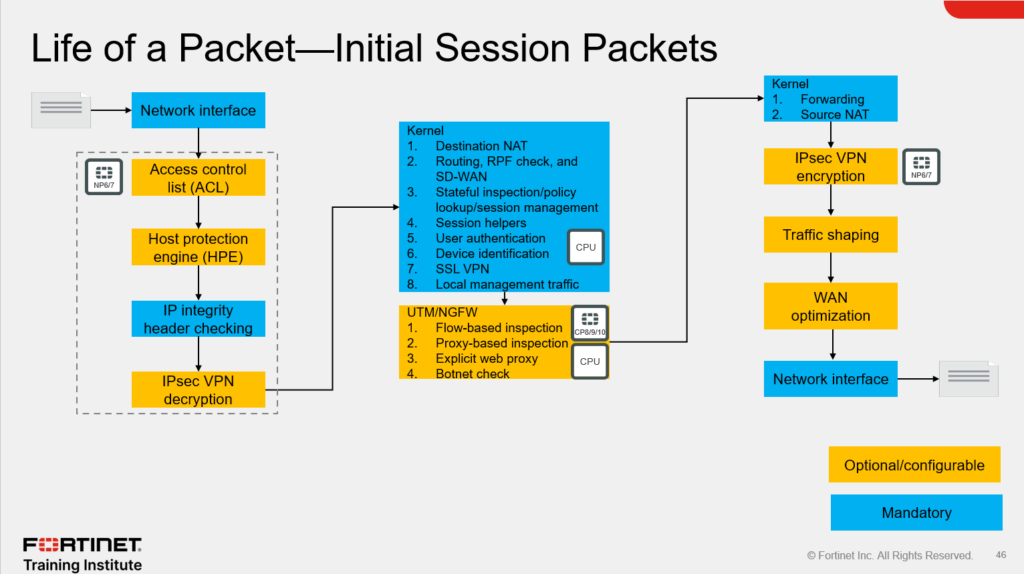
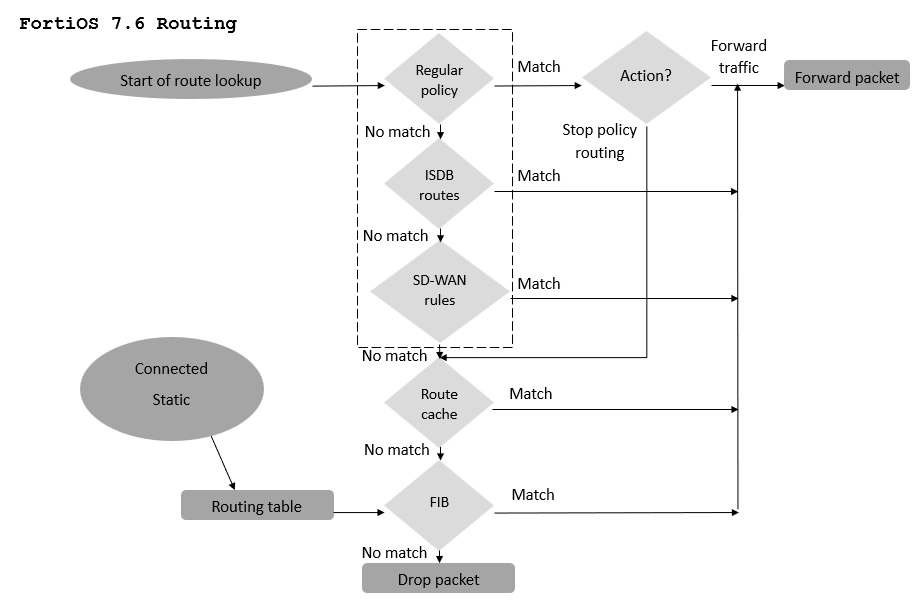
Life of a Packet